Microsoft Sentinel Pricing and Monitoring

When I meet with customers for the first time, the cost of Microsoft Sentinel is a common topic of discussion. I'm updating this blog to reflect recent pricing model changes and include additional pricing considerations. It's important to note that this isn't an analysis of the return on investment for Microsoft Sentinel. However, that's crucial for any organization considering switching to Microsoft Sentinel or using it alongside their current SIEM (Security Information and Event Management) system. The original version of this blog was written in August 2022.
I'm mainly drawing from the Microsoft docs for information in this blog. However, I'm not just echoing what's in the docs and other blogs but also adding my perspective. As mentioned, pricing is a frequent topic in my customer conversations. Now, I always kick off any proof-of-concept talks with this critical discussion. My goal is to provide transparency and clarity to my customers.
The following diagram shows all the elements that feed the cost of Microsoft Sentinel that an organization must consider. I will explain each of these elements in the following paragraphs.
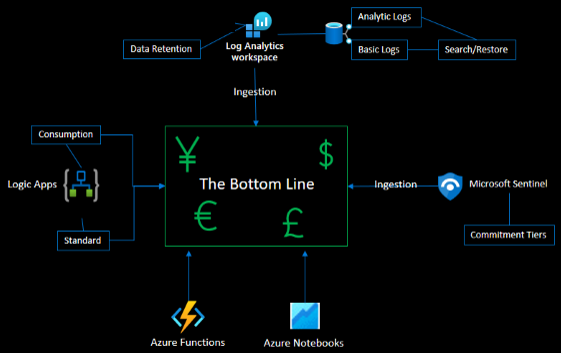
Log Analytics Workspace Ingestion
A Log Analytics workspace is the data store of Microsoft Sentinel. It can exist with or without Microsoft Sentinel. For example, Azure Monitor can set the diagnostic metric to a Log Analytics workspace for analysis. Thus, a separate cost is incurred for data being ingested into the Log Analytic workspace.
Think of it this way. If you have an on-premises SIEM, you must buy storage to support that SIEM. Log Analytics ingestion is how Microsoft charges for that storage in this analogy.
Analytic and Basic Logs
By default, Log Analytics uses Analytic Tables. These logs provide longer retention, no-cost log queries, alerting, and higher ingestion costs. Basic tables provide short retention (8 Days), the cost for limited log queries, and a reduced ingestion cost. For more information on the differences in the log type, check here.
Archive/Search/Restore
From Log Analytics, on a table-by-table basis, you can set a table to move data to Archive. I bring this up in pricing because it does not cost to use Archive, but it does cost to search the Archive and Restore data if necessary.
Retention
The following cost consideration is data retention. You get 30 days of retention with Log Analytics at no cost by default. If you enable Microsoft Sentinel on that Log Analytic workspace, you get 90 days of retention at no cost. But you will still have to manually change the retention settings in Log Analytics to reflect 90 days.
Log Analytic Commitment Tiers
Once you understand how much data you will ingest into Log Analytics for Microsoft Sentinel's analysis. You can utilize commitment tiers to save money on the cost of ingestion. At any time, you can scale up to a higher tier. But you can only scale down after 31 days.
In my latest update to this blog, I want to clarify a fundamental change regarding cost control. If you're using only the Log Analytic workspace without Microsoft Sentinel, your ingestion cost is managed through commitment tiers in Log Analytics alone. But, when we talk about Microsoft Sentinel, the new approach centralizes the use of commitment tiers directly within Microsoft Sentinel itself. To sum it up, the old method required adjusting commitment tiers in both Log Analytics and Microsoft Sentinel. This significant change in how things are done is why I've decided to update this blog.
For more information on all the pricing for Log Analytics, please review the Azure Monitor pricing page.
Microsoft Sentinel Ingestion
As with Log Analytics, Microsoft Sentinel is charged for the amount of data consumption. Just to be clear, the data is not being ingested anywhere else. It is still sitting in the Log Analytic workspace. This is not a double charge. It is charged to provide all the good stuff you can do with the data now that Microsoft Sentinel is looking at it. It may look like ingestion, but you are paying for analytics.
To use another analogy, it is like an all-inclusive resort, sort of. You have paid for the flight (Log Analytic Workspace ingestion) and are now paying for the resort (Microsoft Sentinel). You don't have to pay for food, drinks, or entertainment. The "sort" of part of my comment would be excursions (Logic Apps, Azure Functions, and Azure Notebooks).
There are free connectors. More on that later. You get hundreds of included Analytic Rules, Hunting Queries, Playbooks, and Workbooks. You can create more at no cost. You are not charged for the incidents that are created from the rules.
Microsoft Sentinel Commitment Tiers
In this latest update, I want to highlight a crucial shift in how you can manage costs more effectively. Now, you only need to adjust your expected data ingestion within Microsoft Sentinel. This streamlined approach simplifies the process and helps in containing costs more efficiently. Gone are the days of toggling between different platforms; with this change, Microsoft Sentinel becomes your one-stop hub for managing data ingestion and keeping a close eye on your expenditure.
Logic Apps Consumption and Standard
Microsoft Sentinel is a SIEM and a SOAR (Security Orchestration, Automation, and Response). Automation for Microsoft Sentinel is accomplished with Automation Rules and Playbooks. The Automation Rules don't cost to run, but if they kick off a Playbook or you run a Playbook manually, you will incur a charge.
Playbooks are just Logic Apps triggered by an action like a new incident or alert. An analyst can also trigger the Logic Apps manually to perform such actions as enrichment or notification.
There are two ways to calculate charges: consumption and standard. Consumption is a charge per triggered Logic App. The first 4,000 executions are free. With Standard, you pay for compute hourly, which can be used throughout your single Azure tenant.
With Standard, your organization must determine the demand for Logic Apps, inside and outside of Microsoft Sentinel. Standard may be a better saving if the organization uses many Logic Apps.
Azure Functions
If you plan on using Azure Functions to provide some automation. This would be another cost to consider. Azure Functions supporting Microsoft Sentinel, for example, triggering an Event Hub or Event Grid to import or export data, are used.
Azure Notebooks
Microsoft Sentinel Notebooks are Azure Notebooks, Azure's version of Jupyter Notebooks. This will cost extra if your organization utilizes Microsoft Sentinel Notebooks for deeper machine-learning models or visualization on the logs.
Azure Notebooks use high-performing, machine learning-configured compute to run the notebooks. This is a consumption charge for the use of that compute. Like a typical compute (Virtual Machines), shut it down if you are not running through a notebook. A recent update allows you to establish an auto-shutdown depending on the idle time of the compute resource.
Cost Benefits
Now that I have frightened you with costs, there is good news. There are savings and free logs to get started and see unique insights from your data.
E5 Benefit
If your organization has E5 licensing for Microsoft 365, the organization receives a data grant of up to 5MB per user/day to ingest M365 Data. This data includes the following:
- Azure AD sign-in and Audit Logs
- Defender for Cloud Apps Shadow IT Discovery Logs
- Microsoft Information Protection Logs
- M365 Advanced Hunting Data
Microsoft Defender for Server P2 Benefit
Microsoft Defender for Server is part of Microsoft Defender for Cloud. When using P2 with monitored servers, the organization gets 500 MB/server/day for the following subset of security data types in the logs ingested by Log Analytics:
- SecurityAlert
- SecurityBaseline
- SecurityBaselineSummary
- SecurityDetection
- SecurityEvent
- WindowsFirewall
- SysmonEvent
- ProtectionStatus
- Update
- UpdateSummary
Free Logs
The following logs are always free to ingest into Log Analytics and Microsoft Sentinel:
- Azure Activity Logs
- Microsoft 365 Audit Logs
- Alerts
- Defender for Cloud
- M365 Defender
- Defender for Office 365
- Defender for Identity
- Defender for Endpoints
- Defender for Cloud Apps
Pricing Calculator
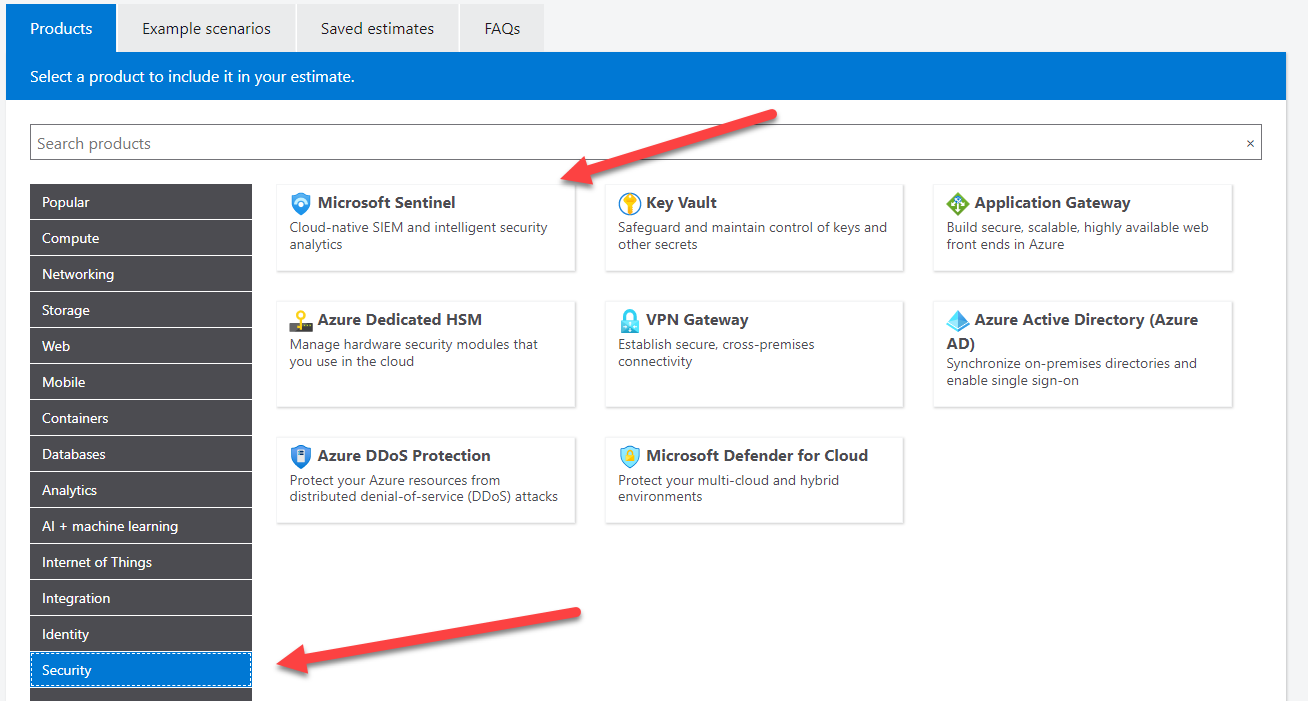
To assist with planning for Microsoft Sentinel costs, check out https://azure.microsoft.com/en-us/pricing/calculator/
You must choose Security and then Microsoft Sentinel to start using the calculator at the bottom of the page.
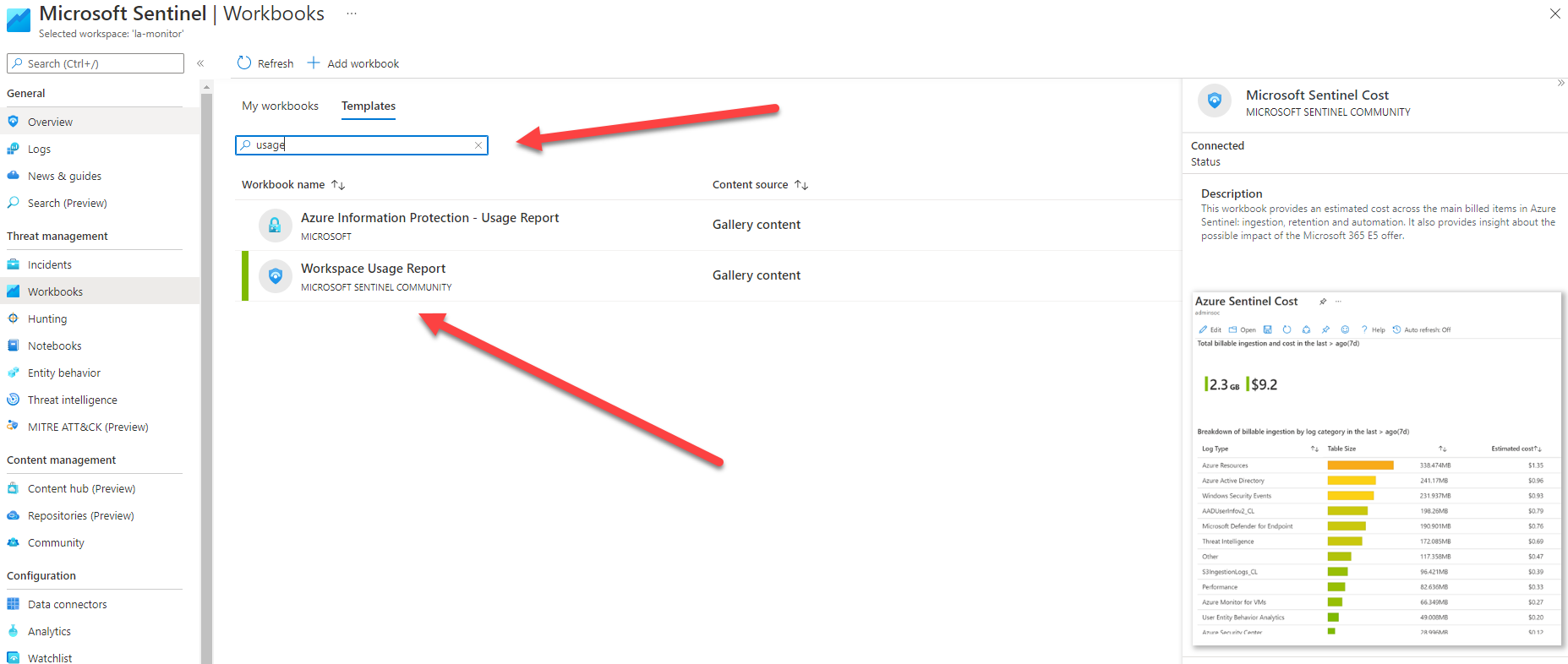
Usage and Cost Monitoring Workbooks
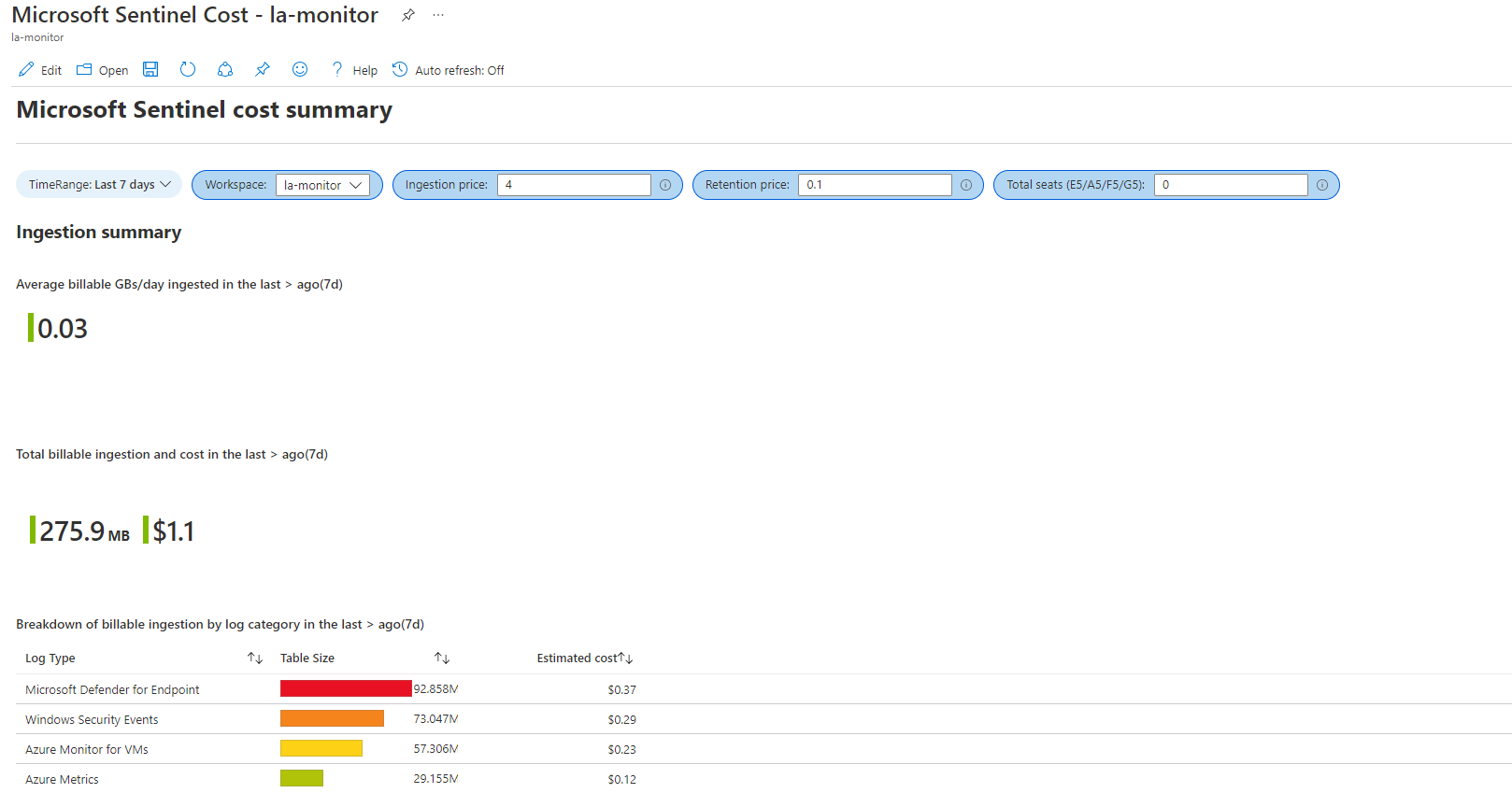
Once you have Microsoft Sentinel up and running, there are a few ways you can monitor your usage and cost by using workbooks.
Microsoft Sentinel Cost Workbook
You should search for cost and save the Microsoft Sentinel Cost workbook to My workbooks. Then View saved workbook.
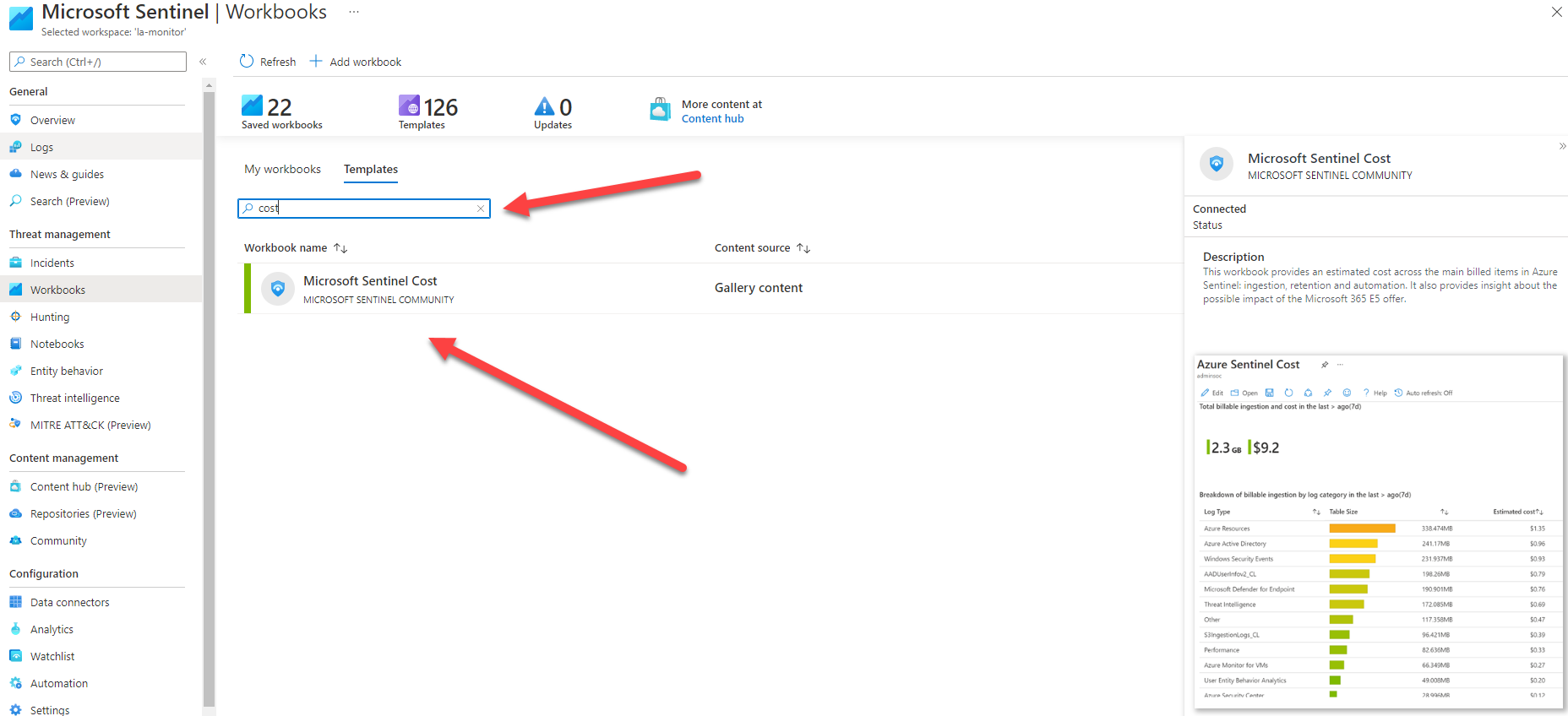
Remember that this is not your actual bill, just an estimate. Set the filters at the top of the page to better predict the pricing. This workbook will provide estimates for ingestion, retention, and Logic Apps.
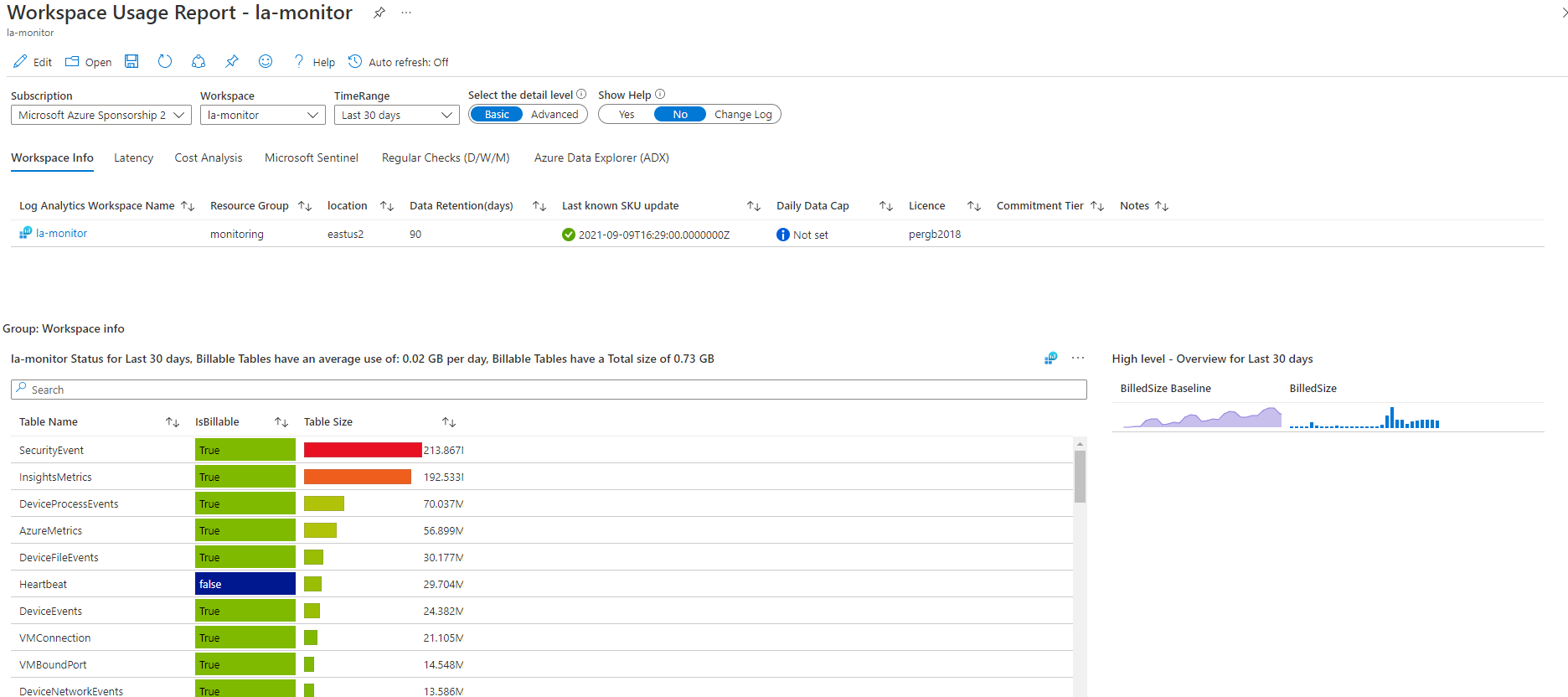
Workspace Usage Report Workbook
The next workbook I suggest you add is the Workspace Usage Report. This workbook will allow you to dig into where your data is coming from to help you determine what needs to be adjusted.
Usage Analytic Rules
Wouldn't it be nice to be notified when things might get out of hand from an ingesting or cost perspective? I am providing links to additional blogs to assist with alerting for cost and usage.
Capping and Alerting on Data Ingestion
Setting a daily cap for data ingestion and building an alert when that daily cap is reached. https://www.verboon.info/2022/05/how-to-analyze-microsoft-sentinel-daily-cap-alerts-aadnoninteractiveusersigninlogs/
Alerting on Daily Ingestion
Rod Trent's blog on alerting when Microsoft Sentinel daily ingestion reaches a threshold. https://azurecloudai.blog/2022/07/07/alert-when-microsoft-sentinel-daily-ingestion-reaches-a-threshold/
Alerting on Sentinel Enablement
Recently, I had a customer who had a significant spike in ingestion for Microsoft Sentinel. After investigating, we determined that someone enabled Microsoft Sentinel on a Log Analytics Workspace that was used to gather application metrics.
You will want to avoid this mistake. This mistake can be costly. Make sure you control who can perform this action. They must have at least the contributor role on the subscription you will enable Microsoft Sentinel.
I have created a KQL query that will return when Security Insights (Microsoft Sentinel) is enabled or disabled on a Log Analytics Workspace. You will want to build a scheduled Analytic Rule out of this query.
//Detects if Microsoft Sentinel has been enabled or disabled on a Log Analytics Workspace.
AzureActivity
| where OperationNameValue in ("MICROSOFT.SECURITYINSIGHTS/ONBOARDINGSTATES/WRITE", "MICROSOFT.SECURITYINSIGHTS/ONBOARDINGSTATES/DELETE")
| where ActivityStatusValue == "Success"
| where _ResourceId has "workspaces"
| extend Activity = case(OperationNameValue == "MICROSOFT.SECURITYINSIGHTS/ONBOARDINGSTATES/WRITE", strcat("Log Analytic Workspace Security Insights Added"), OperationNameValue == "MICROSOFT.SECURITYINSIGHTS/ONBOARDINGSTATES/DELETE", strcat("Log Analytic Workspace Security Insights Removed"), "unknown")
| extend ResourceGroup = tostring(parse_json(Properties).resourceGroup)
| extend x = tostring(parse_json(Properties).resource)
| parse x with ResourceName "/" *
| project TimeGenerated, OperationNameValue, Activity, ResourceGroup, ResourceName, Caller, CallerIpAddress
For more information on Microsoft Sentinel Pricing, check here.
